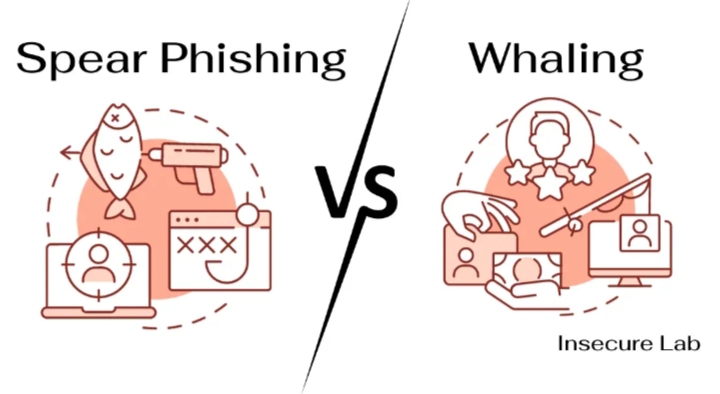
As cyber threats become more advanced, attackers are increasingly focusing on people instead of systems. Two of the most dangerous forms of this approach are spear phishing and whaling. Although both are targeted attacks, they differ in who they aim for and the level of damage they can cause.
What Is Spear Phishing?
Spear phishing is a personalized type of phishing attack aimed at a specific individual or group. Instead of sending mass emails, attackers gather information about their target such as their name, position, or workplace to create convincing messages.
These emails often appear to come from trusted sources, like coworkers or service providers. The objective is to get the victim to click harmful links, open infected attachments, or share sensitive details like passwords. Because the message feels relevant and legitimate, it is often more difficult to identify as a scam.
What Is Whaling?
Whaling is a more focused version of spear phishing that targets high-ranking individuals, such as executives or senior officials. The term comes from the idea of going after “big targets” within an organization.
In these attacks, criminals may pretend to be business partners, legal representatives, or even other executives. They typically request confidential information or urgent financial transactions. Since these individuals have greater authority and access, a successful whaling attack can lead to serious financial and organizational consequences.
Key Differences
The primary difference between spear phishing and whaling lies in the target. Spear phishing can be directed at anyone within an organization, while whaling specifically focuses on top-level leadership.
Whaling attacks also tend to be more sophisticated. Attackers invest more time in research and craft highly convincing messages to avoid suspicion. While spear phishing is already targeted, whaling represents a more refined and high-stakes version of the same tactic.
Why They Work
Both methods succeed by exploiting trust and human behavior. Attackers design messages that seem familiar and credible, often creating urgency to push victims into acting quickly without verifying the request.
Whaling attacks, in particular, take advantage of organizational hierarchy. People are more likely to respond to messages that appear to come from senior executives, making these attacks especially effective.
How to Stay Safe
Protection against these threats involves both awareness and strong security practices. Individuals should be cautious of unexpected messages, even if they seem to come from known contacts, and always verify unusual requests—especially those involving money or sensitive information.
Organizations can strengthen their defenses by using multi-factor authentication, advanced email filters, and strict approval procedures for financial actions. Promoting a culture of verification and caution can significantly reduce vulnerability.
Spear phishing and whaling demonstrate how cybercriminals are shifting toward more targeted and strategic attacks. By focusing on individuals, they can bypass traditional security systems.
Recognizing how these attacks differ and how they operate is essential. With proper knowledge and vigilance, both individuals and organizations can better defend themselves against these sophisticated forms of cyber manipulation.
