As cyber threats continue to grow in complexity, relying on a single security measure is no longer sufficient. Both organizations and individuals need a broader, more resilient strategy that assumes breaches can happen and prepares for them. This is the foundation of defense in depth—a cybersecurity approach built on multiple layers of protection working together.
What Does Defense in Depth Mean?
Defense in depth involves combining various security controls so that if one fails, others remain in place to protect systems and data. Rather than depending on a single safeguard, this method creates overlapping defenses that reduce the chances of a successful attack.
It can be compared to a well-guarded structure with several barriers. Even if one layer is penetrated, additional defenses continue to stand in the attacker’s way.
Why Multiple Layers Are Important
Modern cyberattacks use diverse methods such as phishing, malware, ransomware, and manipulation tactics. No single solution can effectively stop all these threats.
A layered security model provides:
- Backup protection: Other measures remain effective if one fails.
- Slower attacks: Multiple defenses make it harder for attackers to move quickly.
- Better detection: Threats can be identified at different stages, enabling faster response.
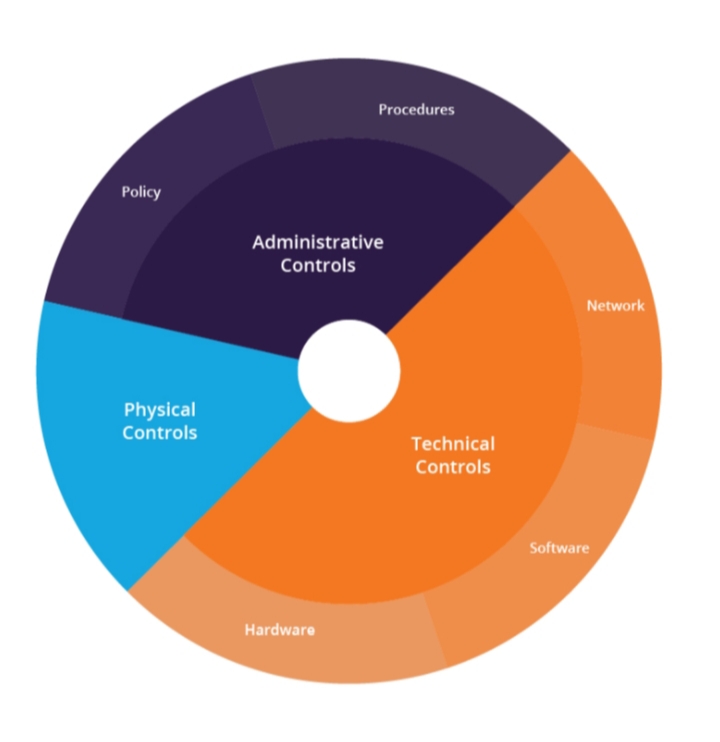
Core Layers of Protection
- Physical Safeguards
Protecting hardware and infrastructure is the first step. This includes controlled access to buildings, surveillance systems, and secured equipment areas. - Network Defenses
Technologies like firewalls and intrusion detection systems help monitor and filter network traffic, blocking suspicious activities. - Device Security
Endpoints such as computers and mobile devices must be protected with antivirus tools, monitoring systems, and regular software updates. - Application Protection
Software should be built and maintained securely. Frequent updates, testing, and secure coding practices help minimize vulnerabilities. - Data Protection
Sensitive information should be secured through encryption, proper classification, and strict access controls. - Access Control and Identity Management
Limiting access to authorized users is essential. Tools like multi-factor authentication and role-based permissions strengthen this layer. - User Education
Since people can be a major point of weakness, training users to recognize threats and follow safe practices is crucial.
Implementation Challenges
Although highly effective, defense in depth can be difficult to manage. It often requires multiple tools, careful coordination, and increased resources. Costs and complexity may rise, but the added security and resilience make it worthwhile.
Tips for Strengthening Your Defense
- Continuously review and improve your security setup.
- Combine preventive, monitoring, and response strategies.
- Keep all systems and tools properly maintained.
- Follow a zero-trust approach verify everything before granting access.
Conclusion
Defense in depth is more than just a technical strategy it represents a proactive way of thinking about security. By using multiple layers of protection, individuals and organizations can better defend against cyber threats and limit potential damage. In an environment where risks are unavoidable, layered security offers a stronger and more dependable defense.
